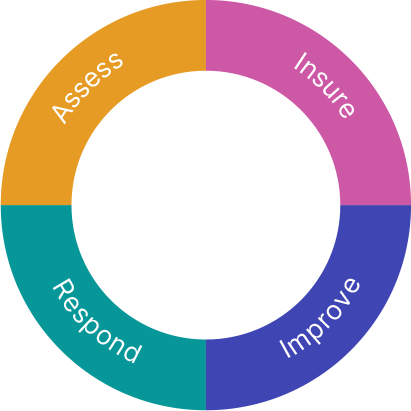
Quantifying risk exposure tells you exactly how much and what types of coverage your business needs. Mapping insurable cyber threats to quantified metrics readily reveals potential cyber vulnerabilities.
- Cowbell Factors™ provide a risk benchmark and a continuous risk assessment against our risk pool of millions of accounts.
- Cowbell Insights highlight vulnerabilities and act as an early detection signal for potential losses.
A standalone Cowbell Prime cyber insurance policy is custom-designed to suit your risk profile. With your Cowbell Factors and your broker, determine insurable threat categories and financial impact.
- AI-assisted continuous underwriting
- Customized coverage
- API-based instant quoting
- Rule-based underwriting referrals
Always ready, the Cowbell Claims Team expedites incident recovery. Cowbell’s security and insurance experts are on-call and always ready to help you immediately with a full range of post-incident recovery services:
- Rapid, informed claims handling
- Claim specialists dedicated to cyber
- Claim insights shared across portfolio
Continuous observation means you can check your risk exposure and progress of your remedial action at any time. Continuous insights allow you to optimize premiums and mitigate risk.
- Cowbell Insights generate continuous, on-demand recommendations.
- Our Risk Engineering Team is available for live, consultative risk sessions. You can also work with one of our partners from the Cowbell Rx marketplace to access a wide variety of security resources.
The 4 pillars powering closed-loop risk management
1
Data Science
A growing pool of 1,000+ inside-out and outside-in data points and risk signals power eight Cowbell Factors.
2
Risk Engineering
Our team of cyber risk experts offer live interaction pre- and post-bind, sourcing hundreds of calls per quarter to avoid hundreds of cyber events.
3
Underwriting
Instant quoting and binding for small risks, with dynamic prioritization of referrals and dynamic assessment for basic risk aggregation and pricing.
4
Claims
Providing fast response times with better information, and rapid follow-through on all aspects of claims to shorten recovery time and decrease claim severity.